Author(s): iamabby#3302
Editor(s): koala#4988
Last updated: 26th Nov 2022
What about Consensus algorithms?
2Blockchain is a decentralized distributed network that provides integrity, transparency, privacy, and traceability. Despite the lack of a centralized government to verify and authenticate transactions, each Blockchain transaction is considered to be 100% secure and validated. A consensus algorithm is a technique used in machine learning to obtain distributed systems or processes to converge on a single data value. These algorithms are intended to ensure reliability in a network with multiple users or nodes. In this way, algorithms achieve consistency in the cryptocurrency network and establish confidence between anonymous users in a pervasive computing environment.
How does it work?
In large-scale, fault-tolerant networks, consensus mechanisms are essential because they allow a group of distributed servers or data centers to communicate and decide on the system state even in the presence of failures or outages. The algorithm establishes a threshold—the limited number of client systems required to gain consensus or agreement to do this.
Consensus algorithms make the assumption that certain systems and processes would be unavailable, and that only certain networks will reply, as they work to solve a consensus problem. In addition, they anticipate that certain transmission errors will occur. On the other hand, the accessible nodes must respond. An algorithm may require at least 51% of nodes to react in order to reach a consensus or agreement on a data value or network state, for example.
Blockchain applications for consensus algorithms
Consensus algorithms have a variety of applications in distributed or decentralized computer networks. Blockchain is currently one of the most widely used applications. Blockchain refers to the distributed ledger best commonly related to bitcoin cryptocurrency. This decentralized database is managed collectively by a decentralized peer-to-peer network of distributed systems or nodes. Consensus methods are used in blockchain networks to get different dispersed nodes to agree. Due to various consensus mechanisms such as proof of work (PoW) or proof of stake, the network is protected because bad transactions cannot be validated by unauthorized users (PoS). Additionally, even when no single node is in control, the technique permits network consensus. Consensus procedures ensure that state machine replicas are synchronized and consistent. They are extremely useful for keeping records and are frequently used to build trust and security across a decentralized computer network, such as blockchain.
Consensus algorithm supports many real-world computing and digital systems including :
-
Google PageRank
-
Load balancing
-
Replication of state machines
-
Smart power grid
-
Clock Synchronisation
Types of Consensus Algorithm
1. Proof of Work (PoW):
One of the original consensus algorithms is the PoW algorithm. The core idea of PoW, first established in 1993 and then again in 2008 by Satoshi Nakamoto, the inventor of Bitcoin, is to have nodes solve challenging mathematical puzzles and make as many guesses as they can in the shortest amount of time. A miner for the following block creation is chosen using this consensus algorithm. This PoW consensus algorithm supports Bitcoin. The primary goal of this algorithm is to quickly and readily provide a solution to a challenging mathematical problem. Due to the high computing demand of this mathematical challenge, the node that can answer it as soon as possible gets to mine the next block.
Miners or validators—also known as participant nodes in blockchains for cryptocurrencies that use the PoW method—must demonstrate that the work they have completed and submitted entitles them to add new transactions to the blockchain. They must solve a difficult mathematical puzzle by discovering the cryptographic hash of a specific block.

Elements of the Proof of Work system:
The success rate of this consensus process can be attributed mostly to two qualities, and they are as follows:
-
Solve the difficult mathematical issue.
-
The accuracy of that solution may be easily confirmed.
Significant problems with the Proof-of-Work consensus
There are some problems with the Proof-of-Work consensus technique:
-
Time-consuming: To locate the accurate result to the riddle that must be solved in order to mine the block, miners must study a great number of nonce values.
-
The verification of a transaction takes ten to sixty minutes.
→ Mine the transaction → add it to the blockchain → commit the transaction
it is not instantaneous.
-
The utilization of resources: In order to solve the challenging mathematical puzzle, miners use a lot of computational power. It results in the loss of resources (money, energy, space, hardware).
-
The 51% risk: If a controlling entity controls 51% or more of the network's nodes, it runs the risk of gaining a disproportionate amount of the network's power, which might lead to blockchain corruption.
Coins that use Proof-of-Work:
-
Litecoin
-
Ethereum
-
Monero coin
-
Dogecoin
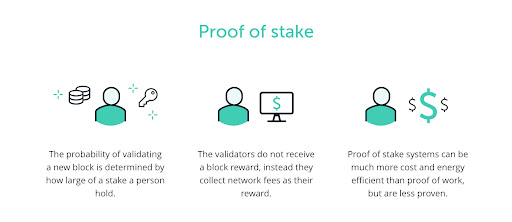
2. Proof of Stake:
Proof of Stake (PoS) is the most widely used alternative to PoW. Ethereum transitioned from a PoW consensus to a PoS consensus. Rather than investing in expensive hardware to solve a difficult challenge, validators in this form of consensus algorithm invest in the system's currencies by staking a portion of their own. The blocks will then be validated by all validators. A validator will validate a block that they believe can be added to the chain by placing a bet on it. Based on the real blocks added to the Blockchain, all validators receive rewards proportional to their stakes, and their stake increases as a result. Based on their financial investment in the network, a validator is ultimately selected to create a new block. As a result, PoS motivates validators to agree through an incentive system. Despite this advantage, the PoS algorithm has a significant disadvantage. A miner who starts with more coins has more control over the consensus mechanism because a validator's mining capacity is determined by the number of tokens they have. Furthermore, because a small number of miners can purchase a large number of coins, the system's decentralisation attribute is diminished.
3. Delayed Proof of Work:
The PoW consensus algorithm has been modified to implement delayed proof of work (dPoW). As part of this consensus technique, the blockchain network takes photos of itself periodically, which are then placed into a block as part of a notarization procedure. Through this approach, the system is completely backed up on the blockchain. Since consensus isn't reached on new blocks using dPoW, it isn't considered a consensus algorithm strictly speaking. Instead, it's a security feature that protects blockchains from a 51% assault, which occurs when one organisation controls the majority of the network's hash rate and severely disrupts operations. This is possible because the dPoW prevents notarized blocks from being restructured by resetting the network's consensus rules every time a block is notarized.
4. Delegated Proof of Stake:
Delegated Proof of Stake (DPoS) is thought to be a more effective and fair variant of PoS. This algorithm is based on a polling system in which participants or witnesses vote for their preferred validators in order to achieve consensus during block production and validation. Delegates, in addition to confirming transactions, help to maintain the blockchain network's stability, transparency, and integrity. Each delegate has an equal number of votes according to the amount of coins they own. Transaction fees are distributed to the respective elected members as payment for their efforts.
5. Proof of Authority:
The Proof of Authority (PoA) consensus mechanism replaces the less scalable and more authority Proof of Work (PoW) consensus algorithm. Furthermore, because block validators stake their reputations and identities rather than money, PoA is a more secure system than PoS. A blockchain network based on PoA is essentially protected by a small number of validating nodes. These nodes are pre-approved and randomly selected trusted individuals who validate blocks and transactions. These users act as system moderators and contribute to the development of a more scalable mechanism than PoW. PoA is ideal for logistical applications such as trade networks and supply chains. Users can enjoy all of the benefits of blockchain technology while protecting their privacy and ensuring the security of their transactions.
6. Proof of Burn:
As a suitable and long-lasting substitute for PoW and PoS algorithms, Proof of Burn (PoB) is currently being tested. PoW and PoB are similar, but PoB consumes significantly less processing power. This is due to the blockchain's lack of hardware or computing requirements for the block validation process. Miners instead "burn" or place currency in the blockchain to establish consensus. Coins are delivered to an address where they cannot be reclaimed, rendering them ineligible and useless. This demonstrates the miners' commitment to the network and gives them the authority to create new coins and approve new network transactions. The likelihood of a miner becoming the next block validator increases as they burn more coins and acquire more mining power.
7. Proof of Capacity:
Instead of burning coins or purchasing expensive gear, validators are expected to invest their hard drive space in the Proof of Capacity consensus. The more hard drive space a validator possesses, the more plausible they are to be chosen to mine the following block and receive the block reward.
8. Proof of Time Spent:
One of the most impartial consensus algorithms, selecting the subsequent block only through impartial ways. In blockchain networks that have permissions, it is frequently employed. Using this process, every network validator has an equal opportunity to create their own block. To accomplish this, after waiting for a variable length of time, each node adds proof of their wait to the block. The produced blocks are broadcast to the network for consideration by others. In the proof portion, the validator with the lowest timer value is declared the winner.
9. PoW/PoS hybrid consensus:
The drawbacks of PoW and PoS algorithms are counterbalanced by a hybrid PoW/PoS technique. To begin, PoW miners add new blocks to a blockchain. After the blocks are formed, the PoS miners decide whether to accept or reject them. During the procedure, they stake some of their tokens, as is done in the PoS algorithm. However, unlike PoS, this hybrid algorithm does not examine the total number of votes cast. Instead, the effectiveness of the new block is determined by a random selection of five votes. If three out of five votes are cast in favor of the block, it is added to the blockchain. PoW miners receive 60% of the reward scheme, PoS miners 30%, and the remaining 10% goes toward system improvement.
10. Different Node Lists (UNL):
Since BFT-tolerant systems typically have considerable latency, Ripple uses "collectively trusted sub-networks" consensus procedures termed "Unique Node Lists" (UNL). To obtain consensus, a node must consult its own UNL rather than the network as a whole. This mechanism allows for less than one-fifth of the nodes to be defective.
11. SIEVE:
Utilizing the SIEVE consensus method, Hyperledger Fabric enables the network to identify and eliminate potential non-deterministic requests while also achieving consensus on the results of the suggested transactions.
Reference: